CommuniTree
TOWARD AN ELECTRONIC BILL OF RIGHTS
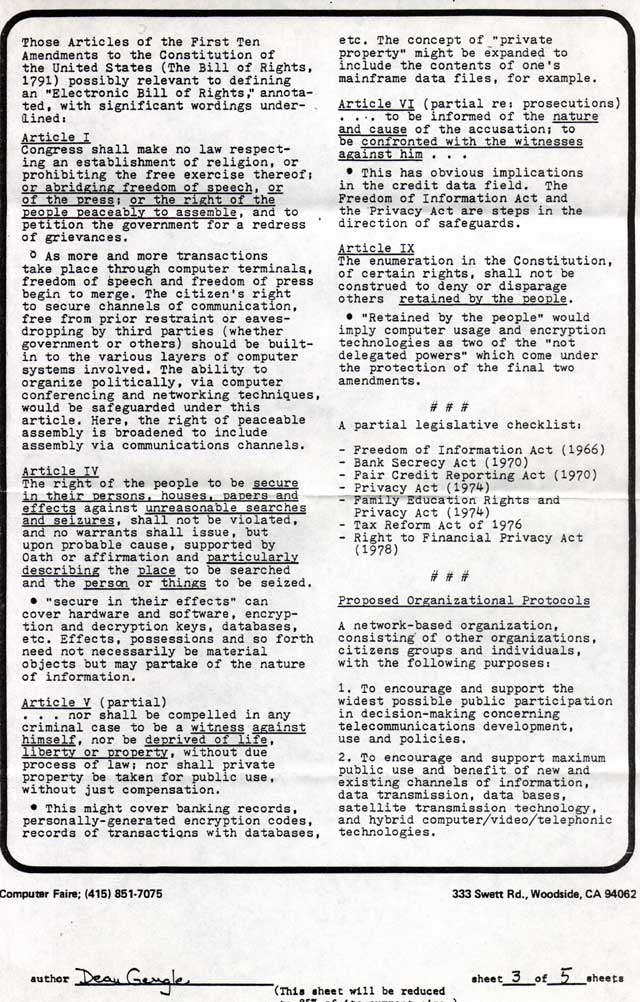
Those Articles of the First Ten Amendments to the Constitution of the United States (The Bill of Rights, 1791) possibly relevant to defining an "Electronic Bill of Rights;'annotated, with significant wordings underlined:
Article I
Congress shall make no law respecting an establishment of religion, or prohibiting the free exercise thereof; or abridging freedom of speech , or of the press; or the right of the people peaceably to assemble, and to petition the government for a redress of grievances.
* As more and more transactions take place through computer terminals, freedom of speech and freedom of press begin to merge. The citizen's right to secure channels of communication, free from prior restraint or eavesdropping by third parties (whether government or others) should be built-in to the various layers of computer systems involved. The ability to organize politically, via computer conferencing and networking techniques, would be safeguarded under this article. Here, the right of peaceable assembly is broadened to include assembly via communications channels.
Article IV
The right of the people to be secure in their persons, houses, papers and effects against unreasonable searches and seizures, shall not be violated, and no warrants shall issue, but upon probable cause, supported by oath or affirmation and particularly describing the place to be searched and the person or things to be seized.
* "secure in their effects" can cover hardware and software, encryption and decryption keys, databases, etc. Effects, possessions and so forth need not necessarily be material objects but may partake of the nature of information.
Article V (partial)
. . . nor shall be compelled in any criminal case to be a witness against himself, nor be deprived of life, liberty or property, without due process of law; nor shall private property be taken for public use, without just compensation.
* This might cover banking records, personally-generated encryption codes, records of transactions with databases, etc. The concept of "private property" might be expanded to include the contents of one's mainframe data files, for example.
Article VI (partial re: prosecutions)
. . . to be informed of the nature and cause of the accusation; to be confronted with the witnesses against him . . .
* This has obvious implications in the credit data field. The Freedom of Information Act and the Privacy Act are steps in the direction of safeguards.
Article IX
The enumeration in the Constitution, of certain rights, shall not be construed to deny or disparage others retained by the people.
* "Retained by the people" would imply computer usage and encryption technologies as two of the "not delegated powers" which come under the protection of the final two amendments.
###
A partial legislative checklist:
- Freedom of Information Act (1966)
- Bank Secrecy Act (1970)
- Fair Credit Reporting Act (1970)
- Privacy Act (1974)
- Family Education Rights and Privacy Act (1974)
- Tax Reform Act of 1976
- Right to Financial Privacy Act (1978)
Proposed Organizational Protocols
A network-based organization, consisting of other organizations, citizens groups and individuals, with the following purposes:
1. To encourage and support the widest possible public participation in decision-making concerning telecommunications development, use and policies.
2. To encourage and support maximum public use and benefit of new and existing channels of information, data transmission, data bases, satellite transmission technology, and hybrid computer/video/telephonic technologies.