Tell~A~Vision = Why Not Try Love Again?
FlyingSnail Links & Archives
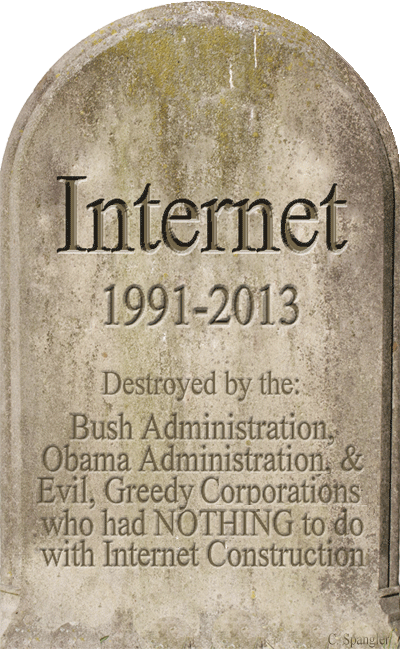
Destroyed by the: Bush Administration, Obama Administration, and Evil, Greedy Corporations who had NOTHING to do with Internet Construction ~ [Click tombstone to see 100 Oldest Registered .COM Domains]
CURRENT THOUGHTS & OPINION
INTERNET = NOPE!
Having survived initial net withdrawal, while continuing to reduce net access, leads me to believe I will eventually be able to get off this compromised, spying, POS known as Internet!
Internet could have resulted in becoming a true treasure for humanity, but unfortunately your owners did not want that to happen.
The proverbial hit the fan when Google insinuated flyingsnail.com was not safe & stated "This site may be compromised. Jul 1, 2012 - Flying Snail - News & Views for Remnants of Paradise ... a strong feminist (and in Russia, utterly alien) message is at the heart of their work." (Screenshot below):

The (above) page in question passed W3C validation and was not "Compromised," as suggested (Screenshot below); proving one can not trust Google comments:
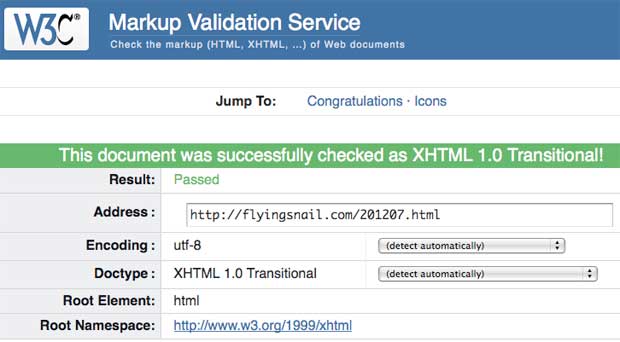
After Google's untrue insinuation, flyingsnail.com access dropped over seventy-five percent (75%) and page rank dropped from 6 to 3.
EMAIL = NOPE!
Unless notified otherwise, those still sending email using banned addresses will need to know the following.
For a slew of reasons all incoming email goes through Guardians.
Email from banned services goes directly into quarantine.
A list of five (5) quarantined emails is sent once a week, which can be rejected or accepted.
There is a master quarantine vault containing thousands of unread mail and "thousands" is 'minimalist speak,' in this case.
On occasion, when an email score is close to passing (yes, there is a scoring system and it constantly improves) a different set of rules 'kick in' and notification is sent. This is why those using a banned email server got a response.
eSHOPPING = NOPE!
This was almost another addiction and at first incredibly convenient; however, it seems to have changed and personally, I no longer trust eShopping or using a phone to shop.
According to recent news, somebody got their hands on millions of US bank PIN numbers and related account information; which appears to mean all those people affected will need to change those PIN numbers, credit cards, debit cards, etc.?
My first bad experiences involved purchasing music for gifts; where the recipient never received the gift, but the store computer said it did. I tried to get this fixed, but it was never rectified, so I stopped trusting that service, let those credit cards expire, and have not used it since.
CORPORATE LIES = YUP!
Lately, there have been outcries from Corporate America who sold out their users and here is the reason why:
It was discovered internal servers in these corporations; specifically the ones POS corporate executives use, were being watched and recorded; meaning it was okay for corporations to hand over user information, but when their own executives were being spied on, they complained.
POS corporations knew spying was being done as far back as the '90s and here is proof directly from the NSA:
http://www.nsa.gov/research/selinux/background.shtml:
SELinux Background~ Researchers in the National Information Assurance Research Laboratory of the National Security Agency (NSA) worked with Secure Computing Corporation (SCC) to develop a strong, flexible mandatory access control architecture based on Type Enforcement, a mechanism first developed for the LOCK system. The NSA and SCC developed two Mach-based prototypes of the architecture: DTMach and DTOS. The NSA and SCC then worked with the University of Utah's Flux research group to transfer the architecture to the Fluke research operating system. During this transfer, the architecture was enhanced to provide better support for dynamic security policies. This enhanced architecture was named Flask. The NSA integrated the Flask architecture into the GNU/Linux® operating system to transfer the technology to a larger developer and user community. The architecture has been subsequently mainstreamed into GNU/Linux® and ported to several other systems, including the Solaris™ (Sun Microsystems/Oracle) operating system, the freeBSD® operating system, and the Darwin (Apple) kernel, spawning a wide range of related work.
In other words, today, unless one is willing to give up all forms of current communication, as well as debit cards, credit cards, anything containing GPS, etc. there is no privacy.
Finally, it is important to remember politicians allow corporations to get away with legal murder, so ... it may be time for a corporate death penalty?
Nonprofit builds tiny houses for Wisconsin homeless
via WVMT, TV ~ Madison, Wisconsin + related video at site.
Here's how data thieves have
captured our lives on the internet
It's not just governments. Companies such as Google and Facebook spy on us too. We have clicked through to their 'free' digital services at the cost of sacrificing our privacy. So how do we get out?
John Naughton, The Observer, Sunday 29 December 2013, Article Source
![]()
Internet surveillance. Everything we do online is tracked. Photograph: Alamy
Whatever else 2013 will be remembered for, it will be known as the year in which a courageous whistleblower brought home to us the extent to which the most liberating communications technology since printing has been captured.
Although Edward Snowden's revelations initially seemed only to document the extent to which the state had exploited internet technology to create a surveillance system of unimaginable comprehensiveness, as the leaks flowed it gradually dawned on us that our naive lust for "free" stuff online had also enabled commercial interests effectively to capture the internet for their own purposes.
And, as if that realisation wasn't traumatic enough, Snowden's revelations demonstrated the extent to which the corporate sector – the Googles, Facebooks, Yahoos and Microsofts of this world – have been, knowingly or unknowingly, complicit in spying on us.
What it boils down to is this: we now know for sure that nothing that you do online is immune to surveillance, and the only people who retain any hope of secure communications are geeks who understand cryptography and use open-source software.
This is a big deal by any standards and we are all in Snowden's debt, for he has sacrificed his prospects of freedom and a normal life so that the rest of us would know what has happened to the technologies on we now depend. We can no longer plead ignorance as an excuse for alarm or inaction.
The scale and intrusiveness of the snooping have been shocking, even to technical experts who understood, in principle, what could be done. From there it is but a short step to demonising the NSA, GCHQ and their partners in surveillance. But to do so is to miss the point.
Security services are military agencies and they do what military forces do, which is to try to accomplish the missions they have been assigned given the resources they have been allocated. Questions about whether the missions are wise, or whether the collateral damage is too high, are above the pay-grade of even the most senior officers.
And since politicians on both sides of the Atlantic insist that everything the NSA and GCHQ are doing and have done is/was done under legal authority and democratic (that is, political) control it follows that the excesses unveiled by Snowden are the consequences of political judgments and misjudgments. Which means that the only way back to more sensible regimes is also a political one. Ultimately, in other words, this is about politics, not technology.
The democratic dilemma
Secrecy impales democracies on the horns of an existential dilemma. On the one hand, democracy abhors secrecy because it makes accountability impossible: citizens cannot consent to what is done in their name if they don't know about it. On the other hand, secrecy is sometimes essential because some things have to be covert – for example activities necessary to ensure the safety of citizens. Societies face a choice between sacrificing accountability; or sacrificing secrecy.
In practice, democracies have fudged the issue by lifting the veil of secrecy just enough to provide a semblance of accountability. In the US, this takes the form of a secret court, with secret hearings and judgments, and a congressional committee, which is pathologically deferential to the intelligence services.
In the UK we have an "oversight" system comprising a deferential Commons committee, together with a couple of retired judges who examine warranted or authorised operations and monitor GCHQ's compliance with the law. This is our semblance of accountability and one of the most important services rendered by Snowden is his exposure of how threadbare it now looks.
To put this point of view to senior British politicians, as some of us have done in the last few months, is to provoke furiously indignant responses. Of course, they insist, they are on top of things. They may not understand the technological details, but they understand perfectly the issues involved and the difficult balances that need to be struck. The boffins and the spooks are on tap, not on top. These ministers (and former ministers) are infuriated by the ignorant questioning of journalists who – unlike those inside the magic circle – don't know what is "really going on". What's more important in explaining the inadequacy of oversight is that most senior politicians in Britain seem remarkably ignorant about IT. A good illustration of this comes from their fond belief that the public would be reassured by the news that GCHQ and the NSA are "only" doing bulk collection of metadata. This was the argument used by William Hague when the Snowden revelations broke and it suggests that our ministers come to the task of regulating digital technology with analogue mindsets.
Metadata are, literally, "data about data". In the case of a mobile phone, they are the numbers called by the handset, the duration of calls, the geographical location of the phone during the call, etc.
In the case of an email, the metadata include the email addresses of sender, addressee, others cc'd, the date and time of dispatch and so on. In web browsing, metadata include a user's clickstream – ie a list of the URLs visited – and the IP address of the computer running the browser. Hague, Sir Malcolm Rifkind et al maintain that collecting metadata is innocuous because it does not involve reading the content of communications. For that a warrant – with the usual supposedly legal procedures and safeguards – is required. So everything is hunky-dory.
This complacency reveals an alarming ignorance of digital technology. In our world of pervasive communications, metadata are incredibly informative. They reveal, for example, everything that one has read online. And everywhere a mobile phone user has been. In a famous case-study some time ago a German politician successfully sued a phone company for his metadata and from it reconstructed an alarmingly accurate, detailed picture of his activities, communications and movements over a period of six months. Hoovering up metadata amounts to invasive, near-comprehensive surveillance.
What's more, it's done without a warrant because of a legal precedent that goes back to the era of analogue telephony – specifically a US supreme court judgment in 1979, which decided that metadata were the property of the telephone company, not of the individual to whose calls the metadata applied. This might have been a reasonable proposition when telephone calls were routed along copper wires, but it's completely inappropriate today. And it is one of the factors that has provided the intelligence agencies with legal immunity.
But the biggest misjudgment of all – the one that legitimised most of the excesses that Snowden has unveiled – was also a political one. It was the decision of the George W Bush administration to declare a "war on terror" in the aftermath of the 9/11 attacks – and the eager adoption by the UK and other allies of the same stance.
As Professor Eben Moglen of Columbia University puts it, the intelligence agencies "presented with a mission by an extraordinarily imprudent national government in the United States, which having failed to prevent a very serious attack on American civilians at home, largely by ignoring warnings, decreed that they were never again to be put in a position where they should have known. This resulted in a military response, which is to get as close to everything as possible. Because if you don't get as close to everything as possible, how can you say that you knew everything that you should have known?" In a real war, one in which the very survival of a state is threatened by a foreign adversary, almost anything is permissible, including the suspension of civil liberties, the right to privacy and all the other things we liberals hold dear. Between 1939 and 1945, Britain was governed by what was effectively a dictatorship wielding unimaginable powers, including comprehensive censorship, the power to requisition private property on demand, and so on. Citizens might not have liked this regime, but they consented to because they understood the need for it.
The "war" on terror is not a war in this sense. It is a rhetorical device aimed at engineering consent for a particular political strategy. But it was enough to provide legislative cover for the acquisition by the US intelligence-gathering agencies of warlike powers, which included the means of surveilling every citizen on earth who had an internet connection, and every owner of a mobile phone in most countries of the world. The war on terror may have succeeded in turbocharging the surveillance capabilities of the US and its allies, but it has also inflicted significant collateral damage on the foreign policy of the US, threatened its dominance of cloud computing and other markets, undermined its major technology companies, infuriated some of its most important allies and superimposed a huge question-mark on the future of the internet as a global system. The war on terror may have made tactical sense in the traumatic months post-9/11. But as a political decision it has had a catastrophic long-term impact.
Surveillance as a business model
Some years ago, when writing a book on understanding the internet, I said that our networked future was bracketed by the dystopian nightmares of two old-Etonian novelists, George Orwell and Aldous Huxley. Orwell thought we would be destroyed by the things we fear, while Huxley thought that we would be controlled by the things that delight us. What Snowden has taught us is that the two extremes have converged: the NSA and its franchises are doing the Orwellian bit, while Google, Facebook and co are attending to the Huxleyean side of things.
In The Master Switch: The Rise and Fall of Information Empires, his magisterial history of the main communications technologies of the 20th century – telephone, radio, movies and television – the legal scholar Timothy Wu discerned a pattern.
Each technology started out as magnificently open, chaotic, collaborative, creative, exuberant and experimental, but in the end all were "captured" by charismatic entrepreneurs who went on to build huge industrial empires on the back of this capture. This is what has become known as the Wu cycle – "a typical progression of information technologies: from somebody's hobby to somebody's industry; from jury-rigged contraption to slick production marvel; from a freely accessible channel to one strictly controlled by a single corporation or cartel – from open to closed system".
The big question, Wu asked, was whether the internet would be any different? Ten years ago, I would have answered: "Yes." Having digested Snowden's revelations, I am less sure, because one of the things he has demonstrated is the extent to which the NSA has suborned the internet companies which have captured the online activities of billions of internet users. It has done this via demands authorised by the secret foreign intelligence surveillance (Fisa) court, but kept secret from the companies' users; and by tapping into the communications that flow between the companies' server farms across the world.
The reason this made sense is because so much of our communications and data are now entrusted to these internet giants. Tapping into them must have seemed a no-brainer to the NSA. After all, Google and Facebook are essentially in the same business as the agency. Its mission – comprehensive surveillance – also happens to be their business model.
The only difference is that whereas the spooks have to jump through some modest legal hoops to inspect our content, the companies get to read it neat. And the great irony is that this has been made possible because of our gullibility. The internet companies offered us shiny new "free" services in return for our acceptance of click-wrap "agreements" which allow them to do anything they damn well please with our data and content. And we fell for it. We built the padded cells in which we now gambol and which the NSA bugs at its leisure.
In our rush for "free" services, we failed to notice how we were being conned. The deal, as presented to us in the End User Licence Agreement, was this: you exchange some of your privacy (in the form of personal information) for the wonderful free services that we (Google, Facebook, Yahoo, Skype, etc) provide in return. The implication is that privacy is a transactional good – something that you own and that can be traded. But, in these contexts, privacy is an environmental good, not a transactional one. Why? Because when I use, say, Gmail, then I'm not only surrendering my privacy to Google, but the privacy of everyone who writes to me at my Gmail address. They may not have consented to this deal, but their email is being read by Google nonetheless. And before any lawyer (or Sir Malcolm Rifkind) pops up to object that having machines read one's communications is not the same thing as having a human being do it, let me gently inquire if they are up to speed on machine-learning algorithms? The fact that Mark Zuckerberg is not sitting there sucking his pencil and reading your status updates doesn't mean that his algorithms aren't making pretty astute inferences from those same updates – which is why Facebook probably knows that two people are going to have an affair before they do; or why one can make interesting inferences about the nature of a couple's marriage from inspection of their network graphs.
And this is where the interests of the NSA and the big internet companies converge. For what they have both managed to do is to abolish the practice of anonymous reading which, in the good old analogue days, we regarded as an essential condition for an open, democratic society. In a networked world, the spooks and the companies know everything you read, and the companies even know how long you spent on a particular page. And if you don't think that's creepy then you haven't been paying attention.
So what is to be done?
All of this we now know – or have belatedly realised – because of Snowden's courage. In less than three decades we have turned a liberating technology into a controlling one. The question now is whether we can extricate ourselves from this mess, or whether we have to resign ourselves to a comprehensively surveilled future?
The answer depends partly on whether we treat the Snowden revelations as evidence of a scandal or a crisis. As the political philosopher David Runciman points out, scandals happen all the time in democracies, but they generate little real change. They pass – and business-as-usual resumes.
Crises, in contrast, do provoke structural change. Our best hope, therefore, is that the Snowden revelations signal a crisis. If they do, then there are some obvious things to be done.
On the technology front, for example, the internet engineering task force needs to reconfigure the network so that every communication on it is encrypted, end-to-end. But, since this crisis has been caused by politics, ultimately only politics can fix it. So we need radically to beef up parliamentary oversight regimes of intelligence services. This requires parliamentarians who are: not awed by spooks or cowed by cant about "national security"; sceptical about the need for surveillance; and advised by truly independent experts. And while some surveillance activities will always need to be covert, activities that are kept secret simply because they would be deemed unacceptable if the public knew about them should be scrapped.
We also need some legislative changes. In particular, the law relating to metadata should be changed. Our metadata belong to us, not to communications providers, and any state monitoring of them should need a warrant. Bulk collection of metadata must end, not only because it threatens democratic values and infringes human rights, but also because it's a wasteful and ineffective way of countering the threats from which it supposedly protects us. And, on the regulatory front, internet companies should be made legally liable for securing any data that we entrust to them.
But finally, and most importantly, President Obama must declare an end to the "war" on terror so that we can all get back to the legitimate and important police work that needs to be done.
John Naughton's book, From Gutenberg to Zuckerberg: What you really need to know about the Internet, is published by Quercus Books. He is currently working on a book about the implications of the Snowden revelations.

Mad Cow Wishing Everyone a Happy New Year from the Crew @ FlyingSnail.com
HAPPY NEW YEAR from Paul Krassner ~ photograph by Nancy CainPredictions for 2014
By Paul Krassner ~ for alternet.org
*Steve Jobs, the late founder and chief designer of the Apple Empire, will be honored posthumously by the Wall Street Journal for morphing the concept of planned obsolescence from a negative aspect of capitalism into a shrewd marketing virtue.
*Toddlers who can turn the pages of an electronic magazine on iPad with the swipe of a finger will get frustrated and have tantrums trying to turn the pages of a physical print magazine.
*Millennials will enjoy watching Avatar on their iPhones.
*Google’s chief executive, Larry Page, will retract his prognostication that “Eventually you’ll have an implant, where you think about a fact, it will just tell you the answer.”
*Jeff Bezos, who is now the owner of both Amazon.com and the Washington Post, will arrange for subscribers to pay extra for having their copies of the Post delivered by drones.
*Chelsea Manning –- formerly Bradley Manning –- will escape from prison with the aid of wealthy supporters. She will be flown to Russia, staying with fellow patriot Edward Snowden until she finds a place of her own. However, Vladimir Putin will interfere with Manning’s asylum, threatening to throw him out. But Manning’s attorneys will then convince President Putin that, since Manning is of the transgender persuasion, having intercourse with a male individual would legally be considered a heterosexual act.
*Dan Savage -- the gay activist who successfully led a mass online prank, landing the word Santorum listed on Google as “1. The frothy mix of lube and fecal matter that is sometimes the byproduct of anal sex. 2. Senator Rick Santorum [infamous for homophobia]” –- will reveal potential presidential candidate Ted Cruz as a user of Viagra, and although Cruz will fail to obtain an erection, his right arm will stiffen and go straight up.
*House Speaker John Boehner will copyright the phrase, “Are you kidding me?”
*The square Hitler-style mustache will replace goatees as a fashion statement.
*Donald Trump will announce that he plans to make a run for the White House in the 2016 election, but inasmuch as he is an admitted germaphobic and therefore wouldn’t like to shake hands with countless strangers in the process, he will conduct his entire campaign wearing latex gloves.
*Campaign finance reform will finally become a reality as the result of a new law requiring all political contributors to remain anonymous.
*The electoral college will be replaced by a system where voters will choose the polling firm they trust the most.
*Mitt Romney will start smoking a pipe to help him portray the imaginary ultra-straight character Bob Dobbs in a movie about Dobbs’ infamously irreverent Church of the Subgenius.
*Cuban President Raul Castro will no longer accept $1 a year as rent for the United States’ prison in Guantanamo Bay. Rather, he will not only demand a million every month, but he will also insist that Barack Obama lift all sanctions. Castro will become angry with his brother Fidel, who ruled Cuba for almost fifty years, and yet he will end up leading a crusade for term limits.
*President Obama’s primary care physician will leave the White House and return to private practice, because he isn’t listed on Obama’s insurance policy network of doctors in his area.
*The Motion Picture Association of America (MPAA) will add a new rating for the film industry: PS, for Predictable Screenplay.
*It will be discovered that the first successful cloning of a human being took place twenty years ago, brought to public attention by his act of suing the scientific team that brought him into an unhappy life. The case will be dismissed as a frivolous lawsuit.
*In a moment of vulnerability, Pope Francis will blurt out from his balcony during a speech to a shocked crowd standing in Vatican Square, “After all, you know, I’m not infallible.”
*A horde of angry apes will ransack the Board of Education in Texas for not allowing evolution to be taught.
*Netflix and Hulu will merge, and along with the growth of binge viewers, a mysterious disease will become known as Netflu.
*Organized crime will attempt to produce counterfeit Bitcoins.
*Inspired by Milo Minderbinder, the entrepreneurial hustler in Joseph Heller’s novel, Catch-22, the Monsanto Company will market genetically engineered chocolate-covered cotton.
*There will be an epidemic of genetically engineered crops being inundated with genetically engineered crop circles.
*Show business celebrity vegetarian converts will include Lady Gaga, who will wear a dress made entirely of heirloom tomatoes, and Meatloaf, who will change his name to Tofuloaf.
*Paranoid hip-hop rapper fans will no longer trust Snopes.com because that website states that Kanye West did not say, “I am the next Nelson Mandela.”
*Louis Uccellini, director of the National Weather Service, will be charged with sexual harassment when he names a tornado Pussy.
*Adolescent boys will trigger a trend across the country with a ritual known as a circle twerk.
*Free online pornography will be allowed in public libraries, but moaning out loud will not be permitted.
*Fetal transplants from poor pregnant girls to wealthy anti-abortion women will become a controversial practice.
*Prescription drugs will serve as a new trend in children’s genderless names, with such examples as Lipitor and Cialis.
*A whistle-blower at the Department of Energy will leak a report concluding that so-called “clean coal” is actually “filthy dirty.”
*Hundred of thousands of jobs will be created as Unemployment Insurance clerks.
*In a surprising change of moral values, The Bank of America will stop doing phone business with the reactionary AT&T. Instead, they will switch to the progressive Credo.
*The Nobel Peace Prize will be secretly awarded to Anonymous.
*North Korea’s beloved young leader will permit 70 McDonald’s restaurants to open all over his dictatorial realm. But, following in his father’s footsteps, he will not allow them to sell any food.
*All around the U.S., Chinese restaurants will substitute the recently popularized word “takeaway” for “takeout” meals.
*A medical team –- the same researchers who concluded that pregnant women who eat peanuts are less likely to give birth to a baby that’s allergic to peanuts -- will visit Mr. Peanut, the logo character of Planter’s Peanuts, wearing a top hat, monocle and holding his elegant cane, in a hospital room where he is severely ill. He will be diagnosed as being allergic to human beings.
*Sociologists and anthropologists will take out a full-page ad in the New York Times condemning the “knockout game” as “utterly barbarian,” just as Conrad Alvin Barrett will be going on trial for assaulting a defenseless African-American man at random for no reason except to capture himself on a selfie cellphone video saying, “The plan is to see if I were to hit a black person, would this be nationally televised?” His lawyers will argue that the charge of a “hate crime” is not “equal justice under the law” because the punishment is more than other attackers in the knockout game are sentenced to. The defense team will further claim that hate crimes are unconstitutional because the law discriminates against racists, that all such crimes are hate crimes, and that the only love crime is an assisted suicide.
*The War on Christmas will continue until Easter, because Jesus will come. He will have a tattoo on the bicep of his left arm. Inside a red heart there will be the letters WWID (What Would I Do). He will stop at a soup kitchen on Skid Row and with the soup he will be given a grilled cheese sandwich. He will be thrilled to see on that sandwich an image of himself as an infant, suckling on his mother’s breast. He will suddenly shout out with joy to his fellow homeless friends: “Happy Holidays!”
*There will be a global competition for the best rationalization by a cult leader when the world doesn’t come to an end on any of those days that they prophesized it would.
*Everybody except you will go viral for fifteen minutes.
flyingsnail.com ~ Disclaimer
1. Be a Fundamentalist -- make sure the Fun always comes before the mental. Realize that life is a situation comedy that will never be canceled. A laugh track has been provided, and the reason why we are put in the material world is to get more material. Have a good laughsitive twice a day, and that will ensure regularhilarity.
2. Remember that each of us has been given a special gift, just for entering - so you are already a winner!
3. The most powerful tool on the planet today is Tell-A-Vision. That is where I tell a vision to you, and you tell a vision to me. That way, if we don't like the programming we're getting, we can simply change the channel.
4. Life is like photography. You use the negative to develop.
5. It is true. As we go through life thinking heavy thoughts, thought particles tend to get caught between the ears, causing a condition called truth decay. So be sure to use mental floss twice a day. And when you're tempted to practice tantrum yoga, remember what we teach in Swami's Absurdiveness Training class: *Don't get even, get odd.*
6. If we want world peace, we must let go of our attachments and truly live like nomads. That's where I no mad at you, you no mad at me. That way, there'll surely be nomadness on the planet. And peace begins with each of us. A little peace here, a little peace there, pretty soon all the peaces will fit together to make one big peace everywhere.
7. I know great earth changes have been predicted for the future, so if you're looking to avoid earthquakes, my advice is simple. When you find a fault, just don't dwell on it.
8. There's no need to change the world. All we have to do is toilet train the world, and we'll never have to change it again.
9. If you're looking to find the key to the Universe, I have some bad news and some good news. The bad news is: there is no key to the Universe. The good news is: it has been left unlocked.
10. Finally, everything I have told you is channeled. That way, if you don't like it, it's not my fault. And remember, enlightenment is not a bureaucracy. So we don't have to go through channels.
Swami Beyondananda's Guidelines for Millennium Enlightenment, Date: Sun, 15 Jul 2001 22:16:48 -0500, Permmalink
Dahbud Mensch ~ Stuck In the Middle With Who
FEMA Concentration Camps
Initiated by Republicans, Continued by Democrats
PERMMALINK for this information
Image Source: http://images.abovetopsecret.com/camplogo.jpg
U.S. CONCENTRATION CAMPS
FEMA AND THE REX 84 PROGRAMThere are over 600 prison camps in the United States, all fully operational and ready to receive prisoners. They are all staffed and even surrounded by full-time guards, but they are all empty. These camps are to be operated by FEMA (Federal Emergency Management Agency) should Martial Law need to be implemented in the United States.
American Concentration Camps
Known Relocation Centers as of January 28, 2000
by M. SmithALABAMA
Opelika - WWII German/Italian POW camp. Under renovation.
ALASKA
Wilds of Alaska - east of Anchorage. No access by road, but there is a railway system. Facility holds 500,000 people. Projection: forced labor camp.
ARIZONA
Florence - WWII German/Italian POW camp. Under renovation.
Ft. Huachua - 20 miles from Mexican border, 30 miles from Nogales Rex 84 Program. Projection: emergency custodial facility.
Pinal County, Gila River - Renovated WWII Japanese-American Special Internment detention facility.
12/9/99 Sedona - Top-secret United Nations (and/or U.S. military) secret military activity near the small tourist town of Sedona, Arizona.
Yuma County, Colorado River - Renovated WWII Japanese-American Special Internment detention facility.
ARKANSAS
Berryville FEMA facility - east of Eureka on Hwy 62. [near Tyson's property.]
Blytheville AFB - was closed; now a camp. Newly constructed wooden barracks surrounded by high barbed wire-topped fencing and guard towers.
Ft. Chaffee - has new aircraft runway and detention facility for 20,000 prisoners.
Jerome, Chicot/Drew Counties - Renovated WWII Japanese-American Special Internment detention facility.
Omaha FEMA facility - on Hwy 65, south of old wood processing plant, on a dirt road that leads to a toxic waste dump.
Rohwer, Descha County - Renovated WWII Japanese-American Special Internment detention center.
CALIFORNIA
Ft. Irwin - Irwin is a remote mountain region south of Death Valley National Monument. Designated as inactive, there is a camp at this facility aprox. 30 miles from I-15 in Barstow.
Manzanar Camp, Inyo County - Deserted WWII Japanese-American Special Internment detention center
Oakdale - Rex 84 Program Emergency custodial facility. 90 miles east of San Francisco on Hwy 120. Holds a minimum of 15,000 people.
Tulelake, Modoc County - Renovated WWII Japanese-American Special Internment detention center.
Vandenberg AFB - Rex 84 Program Emergency custodial facility. Midway between San Lonis Obispo and Santa Barbara on Hwy 1, close to Hwy 101.
COLORADO
Granada, Prowers County - Renovated WWII Japanese-American Special Internment detention center.
Trinidad - WWII German/Italian POW camp. Under renovation.
FLORIDA
Camp Krome - near Miami Dept of Justice detention and interrogation facility.
Elgin AFB - Rex 84 Program Emergency custodial facility. Over 50 miles long, extending from Pensacola Bay to Hwy 331 in De Funiak Springs, adjacent to I-10 on the north, and Ft. Walton Beach vacation spot.
GEORGIA
Camilla, Mitchell County - FEMA facility on mount Zion road aprox. 5.7 miles south of Camilla. From Camilla, take Hwy 19 south, go 5.4 miles from 37/19 Junction to Mount Zion Road, turn left (east) on Mount Zion Road. Not manned or staffed yet.
Ft. Benning - Rex 84 Program Emergency custodial facility east of Columbia, near Georgia/Alabama state line. Prisoners may be brought in via Lawson Army airfield.
Morgan, Calhoun County - FEMA facility. Take I-75 Exit 32 to 300 South to Albany; then Hwy 234 to Morgan; go through Morgan on Hwy 45 South. Facility is 1.5 miles on right (west) side of Hwy 45. Fully manned and staffed, but no prisoners yet.
Oglethorpe, Macon County - FEMA facility 5 miles from Montezuma, 3 miles from Oglethorpe, on west side of Hwy 49. No staff or prisoners yet.
Unadilla, Macon County - FEMA facility on East Railroad Street 1.5 miles from Unadilla on County Rd 230. Plunket Road leads into the facility. Manned and staffed, but no prisoners yet.
IDAHO
Kooskia - 50 plus miles east, near Lolo Pass and Moose Creek, near a landing strip and a national forest. Unmanned.
Minidoka, Jerome County - Renovated WWII Japanese-American Special Internment detention center.
ILLINOIS
Marseilles - small facility on the Illinois River, on Hwy 6, off I-80, relatively close to Chicago. Holds 1400 prisoners. Surrounded by high barbed wire-topped fencing and guard towers.
INDIANA
Ft. Benjamin, Harrison - U.S. Army facility on the outskirts of Indianapolis.
Ft. Wayne - FEMA detention facility.
12/9/99 Grissom Air Force Base - The facility is surrounded by high barbed wire, and lights. These structures are readily visible from US 31.
Indianapolis - massive concentration camp facility on thousands of acres just outside Indianapolis. Includes barracks, razor wire-topped fencing, guard towers, turnstiles, railroad, helicopter landing pads; and what appears to be 3 large furnaces with 3-inch mains on one of the buildings. Under construction.
Terre Haute - FEMA detention facility.
KANSAS
Concordia - WWII German/Italian POW Camp. Under renovation.
Eldorado - Federal prison to be converted to UN forced labor facility. There are 2 that are run by the state: an honor camp by the lake, and a maximum security prison aprox. 1 mile east on US-54. Somewhere in the area is a WWII prison camp, but it has not been located yet.
Leavenworth - U.S. Marshall Federal Holding facility PFP.
Topeka - 80 acres converted to a holding camp for prisoners.
KENTUCKY
Lexington - FEMA detention facility.
Lonisville - FEMA detention facility.
LOUISIANA
Livingston - WWII German/Italian POW camp. Under renovation.
MAINE
Houlton - WWII German/Italian POW camp. Under renovation.
MASSACHUSETTS
Fort Devens - New prison a factory facilities and reservoir that have been built around the camp. It was constructed last year and the railroad had to reconstruct tracks into the prison from Canada and from Boston. Livingston
MICHIGAN
Bay City - on Saginaw Bay surrounded by high barbed wire-topped fencing and guard towers. Connected to Lake Huron. Prisoners may be brought in by water from either the U.S. or Canada.
Central MI - FEMA detention facility.
Detroit - FEMA detention facility.
12/9/99 Fort Custer (near Battle Creek, Michigan) - has a "Prison camp". Also have received reports of FEMA "Box cars" riding the rails through Battle Creek and making stops in or around Fort Custer.
12/9/99 Grayling, National Guard training base - reports of Latvian troops in large numbers (700+) stationed at Camp. All reportees are considered by this Intelligence officer as "very reliable".
Southwest MI - FEMA detention facility.
MISSISSIPPI
Hancock County - NASA facility on old toxic waste dump with 2 camps: one at the end of Kiln Road at Waveland, then the next road after Ammo Road at the Post Office; and one in the center of a rest station back from the Interstate.
[Inmates from the Hancock County Jail claim they have worked details involving the delivery of food to these camps under the supervision of UN guards. One individual claims that one of these camps is full of European men, women and children, all at the same compound. He said that the UN guards were severely beating prisoners, who appeared to be involved in forced labor. It is impossible to verify this information at this time.
MISSOURI
Richards Gebaur AFB, Grandview - large civilian internment facility. AFB personnel are restricted from the area.
12/9/99 Warsaw - Unconfirmed report of a large concentration camp facility.
NEBRASKA
Northeast corner NE - FEMA detention facility.
Northwest corner NE - FEMA detention facility.
Scottsbluff - WWII German/Italian POW camp. Under renovation.
South-central Hastings - FEMA detention facility.
NEVADA
Elco - prison facility 10 miles from Elco.
Las Vegas - From Range Road and Las Vegas Blvd North, across from Nellis AFB, go west on Range Road aprox. 7 miles. Go under I-15 and you'll see a new 6-foot high chain link fence and sliding road gate. Signs say "RESTRICTED AREA. AUTHORIZED PERSONNEL ONLY". Approx. 1 mile after that is the Nevada National Guard compound, and the camp is on the right next to the RR tracks.
Reno - 150 miles south on east side of road, 150 yards from road.
Wells - 40 miles north of Wells in O'niel Basin Area, 25 miles west off Hwy 93.
Winnemucca - at I-80 mile marker 112, 3/4 miles off the road on the south side, near the base of the mountains.
NEW MEXICO
12/9/99 Fort Stanton - currently being used as a youth detention facility approximately 35 miles north of Ruidoso, New Mexico. We do not have a great deal of information concerning the Lordsburg location. However, we have been informed by several people at Holloman AFB near Alamogordo, NM that a new facility was just completed there a few months ago.
12/9/99 White Sands - Missile Range: is being used as a storage facility for United Nations Vehicles and equipment. We have seen them bring this material in on the Whitesands rail spur in Oro Grande New Mexico about thirty miles from the Texas, New Mexico Border.
12/9/99 Holloman AFB - is being very quickly taken over by the German Luftwaft, and they have been doing extensive building, destroying many of the USAF building that have been there for several years.
NEW YORK
Albany - FEMA detention facility.
Buffalo - FEMA detention facility.
Ft. Drum - upstate New York near St. Lawrence River and Lake Ontario, close to Canada. Probable location for eastern processing for prisoners. Both waterways may be used for transport.
Watertown - FEMA detention facility.
OHIO
Cincinnati - FEMA detention facility.
Cleveland - FEMA detention facility.
Columbus - FEMA detention facility.
Lima - FEMA detention facility.
OKLAHOMA
McAlester - WWII German/Italian POW camp. Under renovation.
Tinker AFB, Oklahoma City - civilian detention facility. AFB personnel are prohibited from going near the area, which is under constant guard.
Will Rogers Airport - new FEMA facility. Probable processing center for prisoners west of the Mississippi River.
OREGON
12/9/99 Sheridan - FEMA detention center
12/9/99 Portland - reports that rail boxcars are being built in by FMC corp. that are prisoner transport cars with 144 shackle stations per car.
12/9/99 Umatilla - Prison cells spotted.
PENNSYLVANIA
Camp Hill - off I-15, close to Cumberland Army Depot and Camp Hill correctional facility, across the navigable Susquehanna River from Harrisburg.
Ft. Indiantown Gap Military Reservation - WWII POW camp north of Harrisburg. Renovated by President Jimmy Carter for Cubans during the Mariel boatlift.
TENNESSEE
Crossville - WWII German/Italian POW camp. Under renovation.
12/9/99 Nashville - There are two buildings in Nashville, TN built on State property - that are definitely built to hold prisoners. They are identical buildings - side by side.
TEXAS
Amarillo - FEMA detention facility.
12/9/99 Beaumont Port Arthur area - thousands of acres of federal camps already built on the order of detention camp sesign complete with the double row chain link fencing with the razor styled concertina wire on top of each row. Some but not all of these facilities are currently being used for low-risk prisoners who require a minimum of supervision. However, any of these facilities could be returned into an armed internment detection center within a 24-hr. period.
12/9/99 Ft. Bliss, El Paso - Been undergoing extensive renovation of buildings and from what we have been able to see, many of these buildings that are being renovated are being surrounded by razor wire.
Ft. Hood - newly constructed concentration camp. Surrounded by high barbed wire-topped fencing and guard towers.
Mexia - WWII German/Italian POW camp. Under renovation.
Princeton - WWII POW camp on north side of Denton Hwy. Under renovation.
12/9/99 Ft. Worth - Federal prison under construction on the old Carswell AFB.
UTAH
Millard County - in central Utah, Renovated WWII Japanese-American Special Internment detention center.
Camp Williams, Skull Valley - west of the old bombing range in the south/southwestern portion of Camp Williams. Discovered by a man and his son while rabbit hunting. They were discovered and apprehended.
Utah Lake - 15 miles south of Saratoga Recreation Center 200-300 yds off the road. Surrounded by 40-50-foot high black wire. Made to look something like a golf driving range.
VIRGINIA
Camp A.P. Hill
WASHINGTON
Okanogan County - site for massive concentration camp, bordering Canada. Will be capable of holding hundreds of thousands of prisoners.
12/9/99 Seattle/Spokan West of Vantage - Prison cells spotted.
WISCONSIN
Central WI - FEMA detention facility.
Ft. McCoy - Rex 84 Program Emergency custodial facility in western WI, 30 miles east of Lacrosse, between the point where 90 and 94 intersect.
WYOMING
East Yellowstone - manned facility. Investigators were apprehended by Foreign soldiers. They were unable to identify the language used by the soldiers.
North-central WY - FEMA detention facility.
Park County, Hart Mountain - Renovated WWII Japanese-American Special Internment detention center.
Southeastern WY - FEMA detention facility.
Southwestern WY - FEMA detention facility.
10 Federal Regions
Region I:
Connecticut, Massachusetts, New Hampshire, Rhode Island, Vermont
Regional Capitol: Boston
Region II:
New York, New Jersey, Puerto Rico, Virgin Island
Regional Capitol: New York City
REGION III:
Delaware, Maryland, Pennsylvania, Virginia, West Virginia, District of Columbia.
Regional Capitol: Philadelphia
REGION IV:
Alabama, Florida, Georgia, Kentucky, Mississippi, North Carolina, Tennessee
Regional Capitol: Atlanta
REGION V:
Illinois, Indiana, Michigan, Minnesota, Ohio, Wisconsin
Regional Capitol: Chicago
REGION VI:
Arkansas, Lonisiana, New Mexico, Oklahoma, Texas
Regional Capitol: Dallas-Fort Worth
REGION VII:
Iowa, Kansas, Missouri, Nebraska
Regional Capitol: Kansas City
REGION VIII:
Colorado, Montana, North Dakota, South Dakota, Utah, Wyoming
Regional Capitol: Denver
REGION IX:
Arizona, California, Hawaii, Nevada
Regional Capitol: San Francisco
REGION X:
Alaska, Oregon, Washington, Idaho
Regional Capitol: Seattle
Supplementing these 10 Regions, each of the States is, or is to be, divided into subregions, so that Federal Executive control is provided over every community. Then, controlling the budgeting and the programming at every level is that politico-economic system known as PPBS. The President need not wait for some emergency such as an impeachment ouster. He can declare a National Emergency at any time, and freeze everything, just as he has already frozen wages and prices. And the Congress, and the States, are powerless to prevent such an Executive Dictatorship, unless Congress moves to revoke these extraordinary powers before the Chief Executive moves to invoke them.
Conspiracy Theory with Jesse Ventura ~ Audio repairedSan Francisco Chronicle Acknowledges
ENDGAME By Homeland Security
by William CormierIn a rare breath of fresh air, The San Francisco Chronicle has now written an article confirming concentration camps in the United Sates and the possible impact of "Endgame" - and based on the few comments that were made, people don’t want to believe the truth. Unfortunately, Americans are acting the same as the Jews, disabled, and dissidents did during Hitler’s Third Reich, always believing it could never happen to them… When presented with the evidence that our own government is readying itself to imprison hundreds of thousands, or even millions of patriotic Americans that refuse to support a criminal and perhaps mentally unbalanced President - the author of the article, even though Dan Hamburg is a former Congressman, has been ridiculed for telling the truth: Continue Reading at OpEdNews.com
An Iron Fist In A Velvet Glove
American Democracy Relies on Fascism
by Ted RallBroken or Removed Link
The original link went to:
http://www.columbiacitypaper.com/2008/1/18/american-democracy-relies-on-fascism
which now produces a "Not Found - 404 Error". Here is a replacement link
http://www.informationclearinghouse.info/article18994.htm
What would you do if you learned that Bush Administration officials wanted to round up thousands of Americans and throw them into concentration camps?
For all we know, there is no slippery slope. It’s entirely possible that extraordinary rendition, eliminating habeas corpus, and the torture camps at Guantánamo and elsewhere are exactly what the government says they are–tools for fighting terrorists, not domestic political opponents. But how likely is it?
History is clear: Over and over again, the U.S. government places fascists in powerful positions. Once in office, they exploit wars and national tragedies to roll back hard-won freedoms. They’re Democrats as well as Republicans.
As has happened with increasing frequency in recent years, another blockbuster story revealing the anti-democratic impulse within the top echelon of the U.S. government has appeared and vanished overnight. According to Cold War-era files declassified last week, FBI director J. Edgar Hoover repeatedly advised President Harry Truman to arrest "all individuals potentially dangerous" to national security, jail them in military prisons and try them before kangaroo tribunals that "will not be bound by the rules of evidence."
"For a long period of time the FBI has been accumulating the names, identities and activities of individuals found to be potentially dangerous to the internal security through investigation," Hoover wrote in a 1950 memo. "These names have been compiled in an index, which index has been kept up to date."
Capitalizing on anti-communist hysteria at the start of the Korean War, Hoover asked Truman to preemptively detain 12,000 people, 97 percent of them American citizens, in order to "protect the country against treason, espionage and sabotage."
Hoover was a lunatic. Truman ought to have fired him on the spot. Instead, in September 1950 Congress took his advice and passed a law authorizing the detention of "dangerous radicals" if the president declared a national emergency. Truman signed it. In fact, he declared such an emergency three months later. No one knows why, but the president never actually followed through with mass arrests. Hoover's "subversives"--people suspected of left-wing political sympathies--remained free. He was wrong. There were no acts of sabotage.
It wasn't the first time the government went "crazy."
Between 1919 and 1921 the Bureau of Investigation (predecessor of the FBI) carried out the Palmer Raids, named for Alexander Palmer, Woodrow Wilson's attorney general. The BOI rounded up 10,000 lefties, anarchists and foreigners on a list compiled by a young J. Edgar Hoover, then in charge of the Justice Department's General Intelligence Division. Many were tortured. Five hundred fifty were deported.
Palmer's clampdown accomplished nothing. On September 16, 1920, a bomb attributed to anarchists went off on Wall Street, killing 38 people and wounding over 400.
Crazy...like a fox.
During the 1960s and 1970s the CIA--in violation of its charter, which limits the agency to acting overseas--cooperated with local police departments across the country to compile a list of 300,000 Americans and organizations suspected of opposing the Vietnam War.
On April 6, 1984, President Ronald Reagan signed National Security Decision Directive No. 52. Reagan targeted 400,000 people for arrest and confinement at concentration camps in mothballed Army bases. The National Security Council's "secret government within a government," as Congressional investigators later described it, planned to cancel the 1984 presidential election so Reagan could remain in office indefinitely.
"Lt. Col. Oliver North, for example, helped draw up a controversial plan to suspend the Constitution in the event of a national crisis, such as nuclear war, violent and widespread internal dissent or national opposition to a U.S. military invasion abroad," The Miami Herald reported on July 5, 1987.
People who hate The People never sleep. In 2006 Congress passed the National Defense Authorization Act, which overturns the Posse Comitatus Act of 1878, which prohibited the use of combat troops on the soil of the United States. For the first time in 128 years, the president can declare martial law in case of a hurricane, riot or terrorist attack. In May 2007 Bush attached a National Security Presidential and Homeland Directive to the National Defense Authorization Act. In case of a "national emergency"--the president could declare it without consulting anyone--he could suspend the Constitution and appoint an unelected provisional government under a "national continuity coordinator."
To an optimist, America's brushes with fascism seem like comforting evidence that the system works. Despite it all, even taking into account grotesqueries such as the concentration camps for Japanese-Americans during World War II, the First Amendment remains in force. Few Americans feel threatened by government tyranny. Few worry about getting shot by trigger-happy soldiers or being detained in concentration camps (unless they're flood victims in New Orleans).
So why does a democracy need fascist schemes like Reagan's Rex-84 Alpha Explan (a FEMA plan to put American protesters against a planned war against Nicaragua into camps)? Because American democracy is an iron fist in a velvet glove, a glove that's becoming increasingly transparent.
Threats of repression are rarely carried out. They don't need to be.
If potential opponents are afraid, there's little need for concentration camps. The threat of repression (and actual crackdowns, explained away as exceptional excesses and brushed off with a token apology) creates a chilling effect on people who might pick up a rock instead of a sign.
A dog doesn't have to bite everyone every day to earn a fearsome reputation. Mount cameras all over the place, and you don't need to have anyone actually watching on the other side.
In a country whose legal framework authorizes the government to kidnap, torture and murder them, opponents of U.S. policy must decide whether getting out of line--anything from a letter to the editor to direct action--is worth the risk of getting kidnapped, tortured and murdered.
Ted Rall is the author of the book "Silk Road to Ruin: Is Central Asia the New Middle East?," an in-depth prose and graphic novel analysis of America's next big foreign policy challenge. www.tedrall.com
Rule by fear or rule by law?
by Lewis Seiler and Dan HamburgA clue as to where Harman's commission might be aiming is the Animal Enterprise Terrorism Act, a law that labels those who "engage in sit-ins, civil disobedience, trespass, or any other crime in the name of animal rights" as terrorists. Other groups in the crosshairs could be anti-abortion protesters, anti-tax agitators, immigration activists, environmentalists, peace demonstrators, Second Amendment rights supporters ... the list goes on and on. According to author Naomi Wolf, the National Counterterrorism Center holds the names of roughly 775,000 "terror suspects" with the number increasing by 20,000 per month.
What could the government be contemplating that leads it to make contingency plans to detain without recourse millions of its own citizens?
The Constitution does not allow the executive to have unchecked power under any circumstances. The people must not allow the president to use the war on terrorism to rule by fear instead of by law. Continue Reading at San Francisco Chronicle
Myths of Mass Deception ~ Thanksgiving ~ Christmas
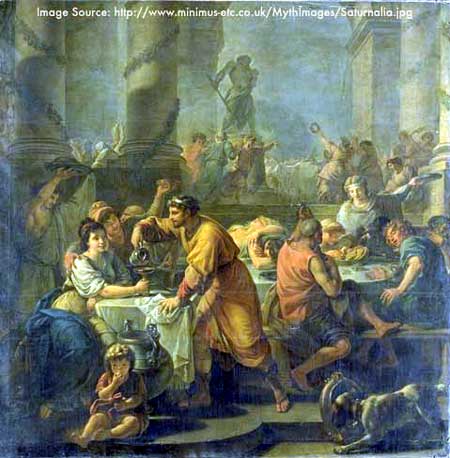
Merry Saturnalia
YOU ARE A PAGAN IF:
YOU BUY A CHRISTMAS TREE AND DECORATE IT
The evergreen tree is a symbol of the green to come at the re-birth of Mother Earth. In ancient Egypt they laid gifts under Palm Trees during the winter celebration. In ancient Rome they used the fir tree (called the Baal Berith) as a testimony to the Pagan messiah, Baal Tamar.
YOU EXCHANGE PRESENTS DURING DECEMBER
The Babylonians celebrated the birth of the God Tammuz on the Winter Solstice and God Nimrod would visit the evergreen trees of the people and leave gifts upon them.
The early Christian Church frowned upon the exchange of gifts because of its Pagan origins. People refused to give up the customs of their old Pagan religions, though. Ultimately, around 700 years ago, the Christian Church decided to attribute the gift exchange to symbolize the gifts given to Jesus by the three Wise Men. It took the Church over 1,300 years to finally "borrow" the Pagan ritual of gift exchanging and call it their own.
YOU KISS SOMEONE UNDER MISTLETOE
The Romans and Saturnalia celebrations are even credited with the tradition of kissing under the mistletoe. Mistletoe was used as a means to get a pretty girl to kiss you during the celebration and ultimately instigate an orgy. The Druids in Scotland and Ireland also believed that mistletoe was a symbol of fertility; a husband and wife desiring a child would hang the mistletoe around their bed during intercourse.
YOU BURN A YULE LOG
The Yule log and Yule Day have Babylonian origins. Yule is the Chaldee name for an infant or little child. December 25th was called Yule Day by Pagan Anglo-Saxon ancestors. The night preceding Yule Day was known as Mother's Night.
YOU CELEBRATE DECEMBER 25th
The Bible does not tell Christians to celebrate the birth of Jesus. The Bible doesn't even tell us when Jesus was born. Of course we can look for "clues" within the gospels to when Jesus might have been born, and people have done that. The assumption of course is that these "clues" are authentic and not stolen from other Pagan mythology.
When the angels appear to the shepherds of Bethlehem to advise them of the birth of Jesus, the shepherds are feeding their flocks at night in the open fields. From late October to early March in Palestine one will encounter bitterly cold weather, icy rain, and sometimes even snow. Tending the flocks, much less tending them at night, is not what one finds Shepherds doing in Palestine (Bethlehem) in the middle of winter. The climate of Palestine dictates that flocks are in the field at night no later than late-October or mid-November and no sooner than early to mid-March. If we base the birth of Jesus on that clue alone, then Jesus would have been born sometime between March and late October.
It is also interesting to note that the Qur'an in Surah 19 talks about the birth of the prophet Jesus. The mother Maryam shakes the trunk of a palm tree (Qur'an 19:25) so that ripe dates fall upon her. Dates ripen in Palestine in the summer.
The Watchtower in December of 1991 stated, "The date of December 25 does not correspond to Christ's birth but to the feast of the Natalis Solis Invicti, the Roman sun festival at the solstice."
The celebration of Jesus' birth on December 25th did not start until 354 CE when Pope Gregory proclaimed the date as that of The Nativity.. Prior to 354 the Church had even guessed Jesus' birth to be in April. After the Church changed the date to December, there were Christians that refused to worship Jesus' birth in December and continued celebrating it in April. They became known as "April's fools."
Why did the Christian Church change the date to December 25th? They changed it because they were having a difficult time converting Pagans that did not want to give up their celebrations of Saturnalia, Natalis Solis Invicti, and Mithraism (among other winter solstice celebrations). Basically the change was made so Christians could say, "Hey look! We have a party, too!"
Another reason for the change to December 25th was not just to coincide with the five-day Pagan festival but also with Hanukkah. Hanukkah occurs on the 25th day of the Hebrew month of Kislev, which occurs usually in December. So by creating a Christian holiday around the same times as Hanukkah and the winter solstice, the early Christian Church was able to convert Pagans and Jews with the lure of a "grand party" to replace the one that the Pagans and Jews already celebrated.
Happy ChanukahPuritans banned Christmas in England during 1552 and you read the disclaimer, didn't you?
It's Beginning To Look A Lot Like Saturnalia
by Judy Andreas
Thanksgiving is nearly forgotten, Sponge Bob Square Pants has floated off into oblivion and the Santa Maria has been replaced by the Santa Claus. The stores are a symphony of Christmas spirit orchestrated by the shopping elf. The presence of Christmas is, indeed, presents. Everyone goes "buy buy." Tis the season to run up credit card debt.
On Black Friday, the Malls became mauls as the word SALE turned the counters into grab bags. Scraggly Santas coaxed children onto laps while cameras clicked a remembrance of this special occasion.
Every year, brains are racked with the annual Christmas quandary........"who" will receive "what." How much can we afford to spend and how much will we wind up spending. Nobody wants to appear cheap. Don't give cash...it's tacky. Gift certificates are a suitable subtle replacement. And, more importantly, they can be charged.
The children, having been groomed by televisions ads, are no longer merely requesting their "two front teeth, " but rather, they have donated their lengthy Christmas "wish lists" to Santa's surrogates.....Mom and Dad. Visions of X-Boxes, rather than sugar plums, dance in their heads. Billions of dollars will be spent on gifts, wrappings, candy, decorations, and greeting cards in the frenzied spending spree that appears to begin earlier every year.
Christmas trees ride on hoods of cars en route to rooms where they will be adorned, ornamented and lit. Christmas stockings enjoy their yearly hangout by the fireplace waiting to be stuffed.
In the midst of this manic merriment and joy to the world, the more contemplative ponder "What is the reason for this season?" Is it the birth of Jesus the Christ, who was born in a manger in Bethlehem on December 25th? How did Christmas devolve into little more than a mandatory ritual of gift exchanging done under the guise of family togetherness and pleasing the kiddiepoos?
Nowhere in the Bible is there any mention of the disciples singing "Happy Birthday Dear Jesus." Nowhere in the Bible is there a command to honor this day. The Bible is strangely silent. And yet, The American Book of Days, George W. Douglas, p. 658, speaks loudly on the topic. "The observance of birthdays was condemned as a heathen custom repugnant to Christians,"
Some well placed googling reveals that the origins of this holiday date back over 4000 years, centuries before the Christ child was born. The twelve days of celebrating, the Yule log, the giving of gifts and carolers going from house to house can be traced back to the early Mesopotamians.
The Mesopotamians were polytheistic. Their chief god was Marduk. Each year, as winter arrived, it was believed that Marduk would do battle with the monsters of chaos. (I cannot help but wonder if Marduk frequented the Palisades Mall in West Nyack) To assist Marduk in his struggle, the Mesopotamians held a festival for the New Year which lasted 12 days.
The ancient Persians and the Babylonians also had a similar celebration which they called Sacaea.
As daylight grew short and the Winter Solstice approached, the early Europeans feared that the sun would not return. Rituals were held to lure back the "Prodigal Sun." In Scandinavia, the return of that warm hearted orb was celebrated with a festival called Yuletide. A feast would be served around a fire burning with a Yule log.
According to some legends, "Christmas" was invented to compete with the pagan celebrations in December. The 25th of December was a sacred day for both the Romans and the Persians, whose religion was Mithraism, one of Christianity's main rivals. The Church adopted many of the Pagan rituals in their attempt to make the religion more attractive to converts.
Google as one may, there is no record of the date of Christ's birth. However, the computer of logic reveals that it is improbable if not impossible that it would have been on December 25th. Since the Biblical account states that the child was born when shepherds were "abiding in the field, keeping watch over their flocks by night" ( Luke 2:8 ), it is unlikely that shepherds in Israel would have been sleeping outside with their flocks during the month of December.
It was not until 350 AD that the Bishop of Rome, Julius 1, chose December 25th as the observance of Christmas. This was obviously influenced by the ancient Romans year end festivities to honor Saturn, their harvest god and Mithras, the god of light. The Roman feast of Saturnalia was a seven-day festival in honor of the deity Saturn. It began on December 17. Saturnalia was considered a fun and festive time for the Romans. As Christianity spread, the Church became alarmed by the continuing practice among its flock of indulging in customs such as this Saturnalian feast. If you can't beat 'em ...join 'em. Slowly but surely, the pagan ritual of using greenery to decorate homes, moved from being prohibited as idolatry to becoming an accepted custom of the festivities. Another tradition at the Saturnalia, involved exchanging candles, clay dolls, and other small gifts.
Did someone say "small?" There's an endangered word and an endangered tradition. "Small" these days describes the size of ones bank account as the calendar flips into January of the new year and people line up at the return counters of their favorite stores.
"Here she goes again, Grinch Andreas"
Not at all. Whether the reason for the season is secular or spiritual, "giving" is a separate issue. With all due respect, however, let's not confuse runaway materialism, avarice and gluttony with the spirit of generosity. Gifts come in all shapes, sizes and elements and are not necessarily located in the material. Gifts need not break the family bank nor the family's back.
Is it difficult to imagine how the gift of time must feel to the lonely?
One year I worked in a soup kitchen in New York City. Watching the endless lines of hungry people coming for their small brown bags broke my heart over and over again. And the only thing I was giving was my time.
Websites such as Giving @ Home suggest a variety of services that provide help for people whose cries would otherwise go unheard. A gift can be something as simple and economical as "listening."
Holidays are Holy Days. There are many ways that we can honor them and one another. Perhaps a little thought might be given to how these occasions can best be spent. A trip to Walmart need not be part of the ritual. - Copyright 2004 Judy Andreas
Attention: FCC ~ Why do television subscribers have to pay for commercials?
Dahbud Mensch ~ Stuck In the Middle With Who
In an attempt to show politicians lie, the following information was originally presented 10 years ago.
It is alleged the first major Spying on US Citizens was specifically done on media personnel & politicians previous to Bush becoming president during 2000. The Patriot Act, that was never read by politicians, was established October 26, 2001.
PERMMALINK for this information
The PATRIOT ACT excretes on the fourth amendment. Simply, anyone doing anything "criminal" can be treated as a "terrorist." Sounds innocuous until you realize that speeding on the highway, on your way to work, is considered to be "criminal."
THE PATRIOT ACT
Brought to you by Republicans,
Supported by Democrats,
&
Nobody Read ItThe Patriot Act Is Not About Terrorism,
It Is About Control of United States Citizens.No mercy in Ashcroft's brand of justice
[Broken Link, Copy Below]Ashcroft's Power Grows In Terrorist Witch Hunt
by Helen Thomas, August 16, 2003
WASHINGTON -- Attorney General John Ashcroft doesn't have enough to do, hunting down terrorists.
With the help of a rollover Congress, he now has a new and bigger club to go after federal judges who impose lighter sentences in criminal cases than he would like.
As a faithful lord high executioner of the administration's much touted "compassionate conservatism," Ashcroft wants to clamp down on those judges.
At issue are the sentencing guidelines laid down by a federal commission that Congress created in 1984. Under pressure from Ashcroft, Congress voted in April to restrict the flexibility of federal judges to depart from the guidelines.
The new law also makes it easier for prosecutors to appeal more cases when they don't like the court-imposed prison sentences.
As it stands now, the attorney general must report within 15 days to Congress the identity of any federal judge who deviates from the rules and the reasons why. And the department must report within five days whether it intends to appeal.
The empowered attorney general then issued an order on July 28 to federal prosecutors, directing them to report all "downward departure" sentencing decisions in criminal cases.
Previously, the prosecutors were required to report to the Justice Department only those sentences that they had objected to and wanted to appeal.
The overall effect is to give Ashcroft more control and the final say on whether to appeal a sentence. And it reduces the powers of the prosecutors in the field, the people who know more about the defendant and the circumstances of the case than does anyone in Washington.
It looks to me as if Ashcroft has designed a new program to intimidate federal judges.
Sen. Edward Kennedy, D-Mass., accused Ashcroft of an "ongoing attack on judicial independence" and said he was requiring federal prosecutors to establish a "black list" of judges who diverge from the guidelines.
Department lawyers say the new rules are in the interest of uniformity. But Ashcroft obviously was miffed that some judges weren't handing out the tough sentences that he wanted.
The sentencing commission has statistics showing that 35 percent of the sentences handed down in federal court in the 2001 fiscal year fell below the guidelines.
Many of those sentences were the results of plea-bargaining and had the approval of the prosecutors.
Jonathan Turley, a George Washington University law professor, said many judges have denounced the guidelines for producing "unduly long sentences" and hampering the courts' ability to fashion punishments to fit the crimes.
Ashcroft wants judges to treat defendants as "statistics rather than individuals," Turley added. In all fairness, Congress shares the blame for giving him even more power to do so.
In his new order to the prosecutors, Ashcroft cited a May 5 speech by Chief Justice William Rehnquist who acknowledged that it was up to Congress to establish guidelines on sentencing policies.
But Ashcroft conveniently failed to mention that Rehnquist also used the same speech to criticize the sentencing restrictions as "an unwarranted and ill-considered effort to intimidate individual judges in the performance of their official duties."
Rehnquist also complained to Sen. Patrick J. Leahy, D-Vt., the top Democrat on the Senate Judiciary Committee, that limiting judicial discretion "would seriously impair the ability of courts to impose just and reasonable sentences."
In a speech last Saturday to the ABA convention in San Francisco, Supreme Court Justice Anthony Kennedy, a moderate conservative, criticized mandatory minimum sentencing and said prison terms were too long. He told the lawyers "our resources are misspent, our punishments too severe, our sentences too long."
He branded the guidelines as "not wise, not just."
An even more dramatic protest against the guidelines came from U.S. District Judge John S. Martin. He quit the bench in Manhattan in June and charged that Congress was attempting "to intimidate judges."
U.S. District Judge Irene M. Keeley of Clarksburg, W.Va., who heads the ABA's National Conference of Federal Judges, supports the critics of the guidelines.
She said the jurists would continue to "evaluate each sentence on a case-by-case basis." A study of the facts will show there is no evidence that judges have been bending the sentencing rules, she said.
Obviously Ashcroft's sense of justice is not the kind that is touched by the quality of mercy.
Ashcroft holds a sign saying, "The Bush Jihad Against The Bill of Rights" and says,
Freedom is Slavery!Target: 'Narco-Terror' [Broken Link. Was:
http://abcnews.go.com/sections/us/WorldNewsTonight/victory_act030820.html]ABCNEWS.com has obtained a draft of the Vital Interdiction of Criminal Terrorist Organizations Act of 2003, or VICTORY Act, which could be introduced to Congress this fall, and which appears to have been prepared by the office of Sen. Orrin Hatch, R-Utah, the chairman of the Senate Judiciary Committee.
Ashcroft says, Uh, yah ... I still need more emergency powers. Our Republic remains endangered.Provisions in the draft would:
Raise the threshold for rejecting illegal wiretaps. The draft reads: "A court may not grant a motion to suppress the contents of a wire or oral communication, or evidence derived there from, unless the court finds that the violation of this chapter involved bad faith by law enforcement."
Melba says, Edith, I hear the Government can tap our phones whenever they damn well want to!!!
Ashcroft who is illegally listening to the conversation says, That's not true, Edith-It's only to catch terrorists!
Edith questions by asking, Melba is a terrorist?Extend subpoena powers by giving giving law enforcement the authority to issue non-judicial subpoenas which require a person suspected of involvement in money laundering to turn over financial records and appear in a prosecutor's office to answer questions.
Ashcroft, while devouring United States Citizens' CIVIL LIBERTIES, demands MORE.Extend the power of the attorney general to issue so-called administrative "sneak-and-peak" subpoenas to drug cases. These subpoenas allow law enforcement to gather evidence from wire communication, financial records or other sources before the subject of the search is notified.
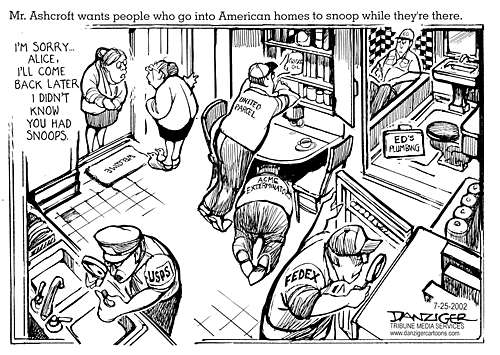
Mr. Ashcroft wants people who go into American homes to snoop while they're there.
~ USPS, FEDEX, UNITED PARCEL, ACME EXTERMINATORS, & ED'S PLUMBING are depicted ~
At the door a woman says, I'm sorry Alice, I'll come back later I didn't know you had snoops.Allow law enforcement to seek a court order to require the "provider of an electronic communication service or remote computing service" or a financial institution to delay notifying a customer that their records had been subpoenaed.
Ashcroft says, IF AT FIRST YOU DON'T SUCCEED.... and is about to blow-up American CIVIL LIBERTIES"This bill would treat drug possession as a 'terrorist offense' and drug dealers as 'narco-terrorist kingpins,' " the aide argued. "To say that terrorist groups use a small percentage of the drug trafficking in the United States to finance terrorism may be a fair point, but this bill would allow the government to prosecute most drug cases as terrorism cases."
John Ashcroft's War on Terrorists ~ A large eye watches a couple in bed, who are trying to sleep.Concluded the aide: "It really seems to be more about a political agenda to jail drug users than a serious attempt to stop terrorists."
WAR ON TERROR thugs destroy a home, hold a gun on a dog, and look at women's
underwear during a raid. Not finding anything terror related, one thug says,
So...As long as we're here... Does your evil kid smoke dope?
Terror Alert ~ Have You Seen This Man (Ashcroft) ? Targets May Include:
* Your privacy rights * Your right to know what your government's up to
* YOUR PROTECTIONS UNDER THE JUSTICE SYSTEM:Ashcroft's Little Secret
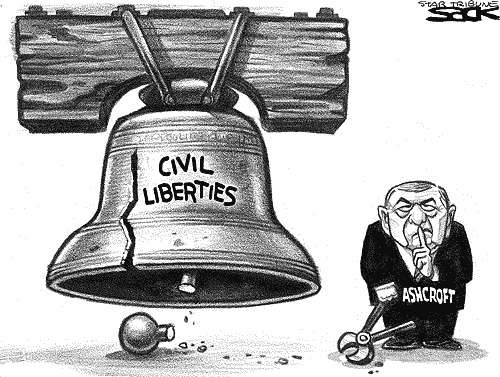
Ashcroft cuts the bell ringer off a Liberty Bell with CIVIL LIBERTIES written on it,
while shushing Americans.Quite simply, Ashcroft's campaign and leadership PAC broke the law by giving and receiving a contribution that exceeded the federal contribution limit by at least 10 times and possibly by more than 200 times, and by failing to disclose the contribution in the first place.
[Broken Link - copy below] ARTICLE COPY:
Alliance for Democracy v. FEC
Is Our Chief Law Enforcement Officer a Criminal?by Lisa Danetz, August 28, 2003
As the top law enforcement officer of the federal government, the Attorney General of the United States has a moral duty to act with honesty and integrity, and to guard his reputation as a law-abiding citizen. This means the Attorney General must -- at the very minimum -- make sure the political committees connected to him follow the nation's campaign finance rules. Respect for the law demands no less.
So why is John Ashcroft stonewalling about charges that his 2000 Senate campaign broke the federal campaign finance law?
A coalition of voters and campaign finance reform groups filed a complaint in March 2001 with the Federal Election Commission (FEC), alleging that Ashcroft's leadership PAC, "Spirit of America," illegally contributed a fundraising list of 100,000 donors to his 2000 Senate campaign in Missouri. Neither the PAC nor the campaign committee reported the contribution.
Spirit of America developed the list of donors between 1997 and 1999 at a cost of more than $2 million, according to a press report. Upon receiving the list at no charge, the Ashcroft campaign allegedly rented the list out and made over $100,000.
If this is true, Ashcroft's PAC and campaign are in hot water on a number of counts. PACs are prohibited from contributing more than $10,000 to federal candidates in an election cycle, and campaigns are likewise prohibited from receiving such contributions. That limit includes the non-monetary donations, like the fundraising list. Further, all PAC contributions must be reported by both the contributing PAC itself and the recipient campaign committee.
Quite simply, Ashcroft's campaign and leadership PAC broke the law by giving and receiving a contribution that exceeded the federal contribution limit by at least 10 times and possibly by more than 200 times, and by failing to disclose the contribution in the first place.
Two and a half years later, the FEC has not resolved the matter, and its file remains secret -- but Ashcroft could ask to open the file to the public. Almost a year ago, a Washington federal judge ruled that plaintiffs could seek consent from Ashcroft's campaign and his leadership PAC to unseal the FEC file. If they agreed, the FEC could release the file.
The plaintiffs wrote letters asking for written consent to allow the documents in the FEC file to be released. They were ignored. Mr. Ashcroft's office also ignored numerous inquiries from the media. In response to a follow-up phone call two months after the letters were sent, Mr. Ashcroft's office confirmed he had received the letter, but again refused to respond.
A month ago, the same federal judge ordered the FEC to explain its delay in handling the matter. The judge's order sets the stage for the case to finally move forward.
Even when the issue is resolved, though, the vast majority of the FEC's file will remain secret unless the Ashcroft groups provide written consent for disclosure. Recognizing this harm, a coalition of campaign reform groups has once more called on the Attorney General to authorize the release of the FEC file. But -- no surprise here -- they, too, were ignored.
If Ashcroft is truly loyal to the rule of law, he will direct his campaign committee and Spirit of America to allow the FEC file to see daylight. Unless, of course, he has something to hide.
© 2003 Lisa Danetz
Lisa Danetz is a staff attorney at the National Voting Rights Institute and the lead counsel for the plaintiffs in Alliance for Democracy v. FEC, a case challenging the Federal Election Commission's failure to act on campaign finance violations committed by political committees controlled by Attorney General Ashcroft.
Is this criminal Ashcroft in Jail?
OF COURSE NOT, HE'S A POLITICIAN!
Republican criminal John Ashcroft representing United States Government as Santa saying,You'd better watch out, You'd better not cry,
You'd better not pout, I'm telling you why
He Taps Your Phone & Reads Your E-Mail Too....He's making a list, He's checking it twice,
Gonna find out who's naughty or nice,
He's Got A File On Everything You Do.He sees when You are sleeping,
He knows when You're awake,
He knows if You've been bad or good,
So Be Good, For Goodness' Sake!
[... of course, with exception to Corporations, who have bought and paid for Politicians.][Reminder: He refers to Government and alleged trusted politicians during the Bush Administration, who sold out US & World Citizens for corporations that moved local labor to foreign countries and constantly get away with murder!]
9 Reasons Wired Readers Should Wear Tinfoil Hats
By David Kravets, November 24, 2011, Article Source
The FBI's Digital Collection System connects FBI offices and telecom providers around the
country to coordinate collection of phone taps for investigations of all sorts.There's plenty of reason to be concerned Big Brother is watching.
We're paranoid not because we have grandiose notions of our self-importance, but because the facts speak for themselves.
Here's our short list of nine reasons that Wired readers ought to wear tinfoil hats, or at least, fight for their rights and consider ways to protect themselves with encryption and defensive digital technologies.
We know the list is incomplete, so if you have better reasons that we list here, put them in the comments and we'll make a list based off them.
Until then, remember: Don't suspect a friend; report him.
Warrantless Wiretapping
The government refuses to acknowledge whether the National Security Agency is secretly siphoning the nation's electronic communications to the National Security Agency without warrants, as the Electronic Frontier Foundation alleges. The lawsuit was based on evidence provided by a former AT&T technician Mark Klein that showed that AT&T had installed a secret spying room in an internet hub in San Francisco. The spying got so bad that Attorney General Ashcroft threatened to resign over it.
When a federal judge said a lawsuit on that issue could go forward, Congress passed legislation stopping the case in its tracks. Two American lawyers for an Islamic charity did, however, prevail in their suit that they were wiretapped without warrants, but the Administration is appealing. Much of the program was legalized in 2008 by the FISA Amendments Act.
The FBI has also built a nationwide computer system called the Digital Collection System, connected by fiber optic cables, to collect and analyze wiretaps of all types, including ones used in ultra-secret terrorism investigations.
Warrantless GPS Tracking
The Obama administration claims Americans have no right to privacy in their public movements. The issue surfaced this month in a landmark case before the U.S. Supreme Court to determine if law enforcement agents should be required to obtain a probable-cause warrant in order to place a GPS tracking device on a citizen's car. The government admitted to the Supreme Court that it thinks it would have the power to track the justices' cars without a warrant.
The invasive technology allows police, the FBI, the Drug Enforcement Administration and other agencies to engage in covert round-the-clock surveillance over an extended period of time, collecting vast amounts of information about anyone who drives the vehicle that is being tracked. The Justice Department has said that law enforcement agents employ GPS as a crime-fighting tool with "great frequency," and GPS retailers have told Wired that they've sold thousands of the devices to the feds.
Tracking Devices in Your Pocket
That mobile phone in your pocket chronicles almost everything. Once-secret software developed by a private company pretty much chronicles all you do on your smartphone and sends it to the carriers. The carriers themselves keep a wealth of information, such as text messages, call-location data, and PINs -- though none of them disclose to their customers what data they store or how long they keep the data.
Law enforcement can get at much of that historical data -- and often get real-time tracking information without proving probable cause to a judge.
Fake Cell Phone Towers
You make a call on your cellphone thinking the only thing standing between you and the recipient of your call is your carrier's cellphone tower. In fact, that tower your phone is connecting to just might be a boobytrap set up by law enforcement to ensnare your phone signals and maybe even the content of your calls.
So-called stingrays are one of the new high-tech tools that authorities are using to track and identify you. The devices, about the size of a suitcase, spoof a legitimate cellphone tower in order to trick nearby cellphones and other wireless communication devices into connecting to the tower, as they would to a real cellphone tower.
The government maintains that the stingrays don't violate Fourth Amendment rights, since Americans don't have a legitimate expectation of privacy for data sent from their mobile phones and other wireless devices to a cell tower. While the technology sounds ultra-new, the feds have had this in their arsenal for at least 15 years, and used a stingray to bust the notorious hacker Kevin Mitnick in 1995.
The Border Exception
The Fourth Amendment doesn't exist along the U.S. border. You know that if you're a close supporter of WikiLeaks or a friend of alleged WikiLeaks leaker Bradley Manning. You're no doubt very familiar with the U.S. government's laptop border search policy, which allows Customs and Border Protection agents to seize and search a laptop belonging to anyone crossing a border into the U.S.
Agents can search through files on a traveler's laptop, phone or other mobile device, read e-mail or view digital snapshots to uncover incriminating evidence, and they don't need any reason to do so.
The government argues, and the 9th U.S. Circuit Court agrees that searching through a person's laptop for copyright violations is no different than looking through their suitcase for cocaine -- and thus fits squarely with what is known as the 'border exception' to the Fourth Amendment. That means a border agent doesn't need reasonable suspicion, probable cause or even a hunch to open your laptop, seize it and make copies of your data.
At least three supporters of WikiLeaks, including security researcher Jacob Appelbaum. have been subject to the policy and had devices seized and searched as they re-entered the U.S. from foreign trips. U.S. Customs and Border Patrol seem to particularly like searching Appeblaum's devices and questioning him, despite the fact that Wikileaks has never been charged with a crime in the U.S..
The "6 Months and It's the Government's" Rule
If you're already not wanting a dose of Prozac, consider that the law allows the government to obtain Americans' e-mails, without a warrant, if it's stored on some other company's servers for more than six months. The Electronic Communications Privacy Act, adopted in 1986, turned 25 this year. When written, the law assumed e-mails left on a server for that long were abandoned.
In the age of Gmail, that's simply ridiculous. A proposal to demand a court warrant for any and all e-mail never got a Senate hearing and was opposed by the Obama administration.
The Patriot Act
No paranoia list would be complete without including the Patriot Act, the now 10-year-old law adopted in the wake of September 11. The act, which has remained largely the same since former president George W. Bush signed the legislation six weeks after 9/11, gives the government, among other things, the power to acquire phone, banking and other records via the power of a so-called "national security letter," which does not require a court warrant.
National security letters, perhaps the most invasive facet of the law, are written demands from the FBI that compel internet service providers, financial institutions and others to hand over confidential records about their customers, such as subscriber information, phone numbers and e-mail addresses, bank records and arguably websites you have visited.
The FBI need merely assert, in writing, that the information is "relevant" to an ongoing terrorism or national security investigation. Nearly everyone who gets a national security letter is prohibited from even disclosing that they've received one. More than 200,000 letters have been issued by the FBI, despite a series of stinging reports from the Justice Department's internal watchdog, who found FBI agents weren't just routinely sloppy; they also violated the law.
Moreover, a decade after Bush's signature, information is sketchy about how the law is being used in practice. For instance, Sen. Ron Wyden (D-Oregon) claims the government applies a far broader, and classified, legal interpretation of the Patriot Act's power to let the government seize most anything it deems relevant to an investigation (Section 215).
"We're getting to a gap between what the public thinks the law says and what the American government secretly thinks the law says," the Senate Intelligence Committee member said in a recent interview with Wired. "When you've got that kind of a gap, you're going to have a problem on your hands."
Government Malware
It's little known, but governments have their own malware/spyware that it deploys against suspected lawbreakers. The FBI's version, the last time we checked, was called CIPAV. Once an FBI agent convinced a target to install it (by clicking an e-mail attachment or link on the web), the spyware reports back everything that computer does online.
German states recently came under fire for misusing a similar program that reportedly could turn on a computer's camera and take screenshots. And a recent Wall Street Journal story catalogs a surveillance software company which trumpeted its ability to infect users via a fake iTunes update. The company sells its wares to governments around the world.
Known Unknowns
Former Secretary of Defense Donald Rumsfeld took an unfair amount of abuse for his deployment of the phrase "known unknowns." And it's these known unknowns that might be the most disturbing part of the list. For instance, does the government think the Patriot Act allows it to force Google to turn over information about anyone who has searched for certain keywords using orders that come with a gag order? Is the NSA sucking up everything we say on our phones and that we do online, under the theory it pushed in a court case that it's not a search until a human actually looks at the data? How often do police investigating a crime ask wireless providers to give them a list of all the people whose phones were in use in the area when they think a crime was committed? What kind of sweeping surveillance orders have been issued under the 1998 law that Congress passed to legalize much of the warrantless wiretapping of Americans? And finally, how long is the government storing all this data, and how can we be sure that our future governments won't start using this data to target Americans based on activities protected by the First Amendment?
And no -- a tinfoil hat won't help you at all.
Drop Dead ~ Telecom Crimes ~ Denialist ~ He Said It ~ Rethinking 9/11 ~ Are you better off?
Call For New Corporate Top-level domain: nsa
Examples of Possible Second-level domain names:
google.nsa | apple.nsa | microsoft.nsa | facebook.nsa | aol.nsa | at&t.nsa | yahoo.nsa | snapchat.nsa | sunmicrosystems.nsa | verizon.nsa | paltalk.nsa | skype.nsa | twitter.nsa | youtube.nsa | gnu/linux.nsa | freeBSD.nsa | solaris.nsa | apple/darwin.nsa | etc.
Integrity ~ From Wikipedia, the free encyclopedia
Integrity is a concept of consistency of actions, values, methods, measures, principles, expectations, and outcomes. In ethics, integrity is regarded as the honesty and truthfulness or accuracy of one's actions. Integrity can be regarded as the opposite of hypocrisy, in that integrity regards internal consistency as a virtue, and suggests that parties holding apparently conflicting values should account for the discrepancy or alter their beliefs.
Hypocrisy ~ From Wikipedia, the free encyclopedia
Hypocrisy is the state of pretending to have virtues, moral or religious beliefs, principles, etc., that one does not actually have. Hypocrisy involves the deception of others and is thus a kind of lie.
Judas Iscariot ~ From Wikipedia, the free encyclopedia
Judas Iscariot is infamously known for his kiss and betrayal of Jesus to the hands of the chief Sanhedrin priests in exchange for a payment of thirty silver coins. His name [Judas] is often used to accuse someone [or a corporation] of betrayal.
From: http://www.nsa.gov/research/selinux/background.shtml:
SELinux Background ~ Researchers in the National Information Assurance Research Laboratory of the National Security Agency (NSA) worked with Secure Computing Corporation (SCC) to develop a strong, flexible mandatory access control architecture based on Type Enforcement, a mechanism first developed for the LOCK system. The NSA and SCC developed two Mach-based prototypes of the architecture: DTMach and DTOS. The NSA and SCC then worked with the University of Utah's Flux research group to transfer the architecture to the Fluke research operating system. During this transfer, the architecture was enhanced to provide better support for dynamic security policies. This enhanced architecture was named Flask. The NSA integrated the Flask architecture into the GNU/Linux® operating system to transfer the technology to a larger developer and user community. The architecture has been subsequently mainstreamed into GNU/Linux® and ported to several other systems, including the Solaris™ (Sun Microsystems/Oracle) operating system, the freeBSD® operating system, and the Darwin (Apple) kernel, spawning a wide range of related work.
Images Via Wikipedia, the free encyclopediaWhy? = Because Loyal Users Should Know Who Sold Them Out
The National Security Agency has obtained direct access to the systems of Google, Facebook, Apple and other US internet giants [who sold out their users?].
The NSA access was enabled by changes to US surveillance law introduced under [Republican] President Bush and renewed under [Democrat] President Obama in December 2012 ~ via Dahbud Mensch
Z.. Unfinished Story
Once upon a time ~ Click to view picture story in progress
Notes from ~@~
Living Wage End of the Year Celebration
Saturday, Dec. 14, 2013 ~ 4 p.m. to 7 p.m.
2940 – 16th Street, (between Mission and South Van Ness)Date: Sat, 30 Nov 2013 20:21:21 -0800
From: sflivingwage
To: sflivingwage
Subject: [sflivingwage] Dec. 14 End of the Year CelebrationCome and support the Living Wage Coalition. I'll be performing some original songs (see below) and would love to see you there.
John Radogno
Español sigue
You are invited to the
Ud. Esta Invitado a LaLiving Wage End of the Year Celebration
Celebración de Salario Digno del Fin de AñoLet’s Celebrate, Reunite and Continue the Fight!
Celebremos, Unamonos y Continuemos Luchando.Music! Spoken Word! Food! Raffle!
Musica! Poésia! Comida! Rifa!Saturday, Dec. 14, 2013 ~ 4 p.m. to 7 p.m.
Sabado, 14 de Dic. ~ 4 p.m. a 7 p.m.2940 – 16th Street, (between Mission and South Van Ness)
2940 Calle 16th (entre Mission y South Van Ness)San Francisco
$5 for program – children under 10 free
$ 5 por programa - niños menores de 10 años gratis$5 dinner – $3 for children under 10
$5 por la cena – $3 para niños menos de 10 añoschildcare available – contact us to reserve
cuidado de niños disponible – llamarnos para reservarmusic by
musica deDiana Gameros
Duo Pizzicato – Martha Hawthorne and Bill Foss
Tommi Avicolli Mecca
John Radogno
Una Flor, Un Canto y Una Poesia – Elizabeth Esteva, Nancy Esteva and Mario Esteva
poetry by Alfonso Texidor, Cesar Love, Alice Rogoff, Yolanda Catzalco, and Po’ Poets
poèsia de Alfonso Texidor, Cesar Love, Alice Rogoff, Yolanda Catzalco, y Po’ PoetsFor more information, contact SF Living Wage Coalition, at 415-863-1225 or
www.livingwage-sf.org
Para más informacion, llame SF Living Wage Coalition, a 415-863-1225
PPRS - Pacific Packet Radio Society - Historic Wireless Digital Communication
Wireless Digital Communication
Was First Introduced in the United Statesby Dr. Hank Magnuski, Co-founder of the Pacific Packet Radio Society,
December 10, 1980
Pacific Packet Radio Society gateway | history | photos | papers | links | packet audio | videoPacific Packet Radio Society
33rd Anniversary
Historic KA6M Digital Packet Radio Repeater
First United States Wireless Data CommunicationsDear Packet Radio Enthusiast,
Thanks very much for the letter of inquiry which you sent me. The response I've received to the initial publicity about the packet repeater has been very enthusiastic, and I have been deluged with requests from hams, both locally and from various points around the country, for more information about the repeater, for schematics, for listings, specifications, modems, proms, SDLC chips, Vancouver boards, and for talks at clubs. Needless to say, all this activity, plus continuing development on the packet hardware and software has kept me very busy, and I apologize for the long delay in responding to your letter. Let me bring you up to date on what has happened, or is happening, since the initial announcement of the repeater, which went on the air in December of 1980.
In the early months of this year, the packet repeater was operating out of my residence, and was still an experimental machine. Since then, we have installed a couple of upgrades to the control software, we have used a better CPU card, increased the power level, moved the repeater to 700 feet elevation, and integrated its operation to be 100% compatible with the protocol used by the Vancouver Digital Communications Group (VADCG). The repeater has changed from being a laboratory curiosity to a major Bay Area repeater heard from Berkeley to south San Jose, and the user community has grown from a couple of stations to a network of some 30 users. The packet system here now has a mailbox on-line 24 hours a day, several on-line personal computers, and network links (courtesy of a commercial packet network) to the other active packet radio centers in Vancouver and Ottawa. We have also just installed an HF port on 20 Meters, and are beginning some experiments aimed at establishing connection with AMRAD in Washington and with equipment located at W1AW.
VADCG TNC built by C. Spangler - PPRS photosMost of the original packet radio experiments were done in Canada (in part due to the Canadians' pioneering communications spirit, and in part due to less restrictive regulations up there), and three main centers were at work: Montreal, Ottawa and Vancouver. The technology employed by each of these groups differed, and each approach has its own merits. My thinking and ideas very closely paralleled the work started by Doug Lockhart, VE7APU, and I can best report on what is happening with groups which have adopted HDLC (High-level Data Link Control) framing as the basis of their protocol. The HDLC/ SDLC frame is a new, universally accepted standard in the data communications industry, and Doug and I feel it offers a good starting point on which to build a packet radio network. As it turns out, groups in Washington D.C., Los Angeles, El Paso, Denver, Sacramento, and Hamilton have also taken up this technology, and it is likely that we already have a sufficient number of people using this technique that it will become the defacto standard in the amateur radio community.
It would be impossible for me to completely describe the protocol and equipment being used in this letter, so I will briefly cover some of the topics and give you some pointers on where to find additional information. As you might guess, this is a new area for amateur radio, and tutorial material and handbooks simply do not yet exist. Many issues and problems remain to be discussed, and there is opportunity to make substantial contributions to the state of the art. [Snip] [Continue Reading] - Thanks again for your interest. See you on the net. Best regards, Hank Magnuski, KA6M - [More Papers and History]
Boptime with Even Steven + The Legends of Wilmington Jazz

Saturday, 6 AM Eastern time, 3 AM Pacific time:
MP3 Stream ~ Low 24K ~ High 128K ~ Real Audio ~ Low 24K ~ High 128K ~ Windows ~ Low 24K ~ High 128K
ARPSN Seismic Heliplots ~ Seismic Activity & Weather at Seismic Site
M 3.6 - Northern California - 2013-12-06 06:44:54 UTC
13 km NE of Angwin, United States / pop: 3,051 / local time: 22:44:54.0 2013-12-05 Depth 10 km
M 3.5 ~ Northern California ~ 2013-12-05 10:57:29 UTC ~ 38.79 N ; 122.78
6 km SW of Cobb, United States / pop: 1,778 / local time: 02:57:29.9 2013-12-05 Depth: 3 km
Mike Wilhelm ~ Charlatans, Flamin' Groovies, Loose Gravel, and more
Guns & Robbers w/Mike Wilhelm
(of Hired Guns, Charlatans, & Flamin' Groovies fame)Saturday, December 7, 2013 from 8 to 10 PM PST
(door opens 7:00 PM)Art House Gallery & Cultural Center
2905 Shattuck Ave., Berkeley, CA 94705
(between Russell and Ashby)
For reservation: call 510-472-3170A solo acoustic concert of blues & other musical Americana by the guitarist, Blues Hall of Fame Inductee & founding member of the first San Francisco psychedelic band, the Charlatans. Great American Robber Barons featuring Diana Mangano (Jefferson Starship) & Keith Dion ( Noel Redding, Ponsonby DCs) open with an acoustic set.
Karl Cohen ~ Association International du Film d'Animation-SF Newsletter
ASIFA~SF NEWSLETTER
Association International du Film d'Animation
(International Animated Film Association)
December 2013Highlights include:
REVIEW OF A NEW FORM OF AN ANIMATED DOCUMENTARY - "IS THE MAN WHO IS TALL HAPPY? AN ANIMATED CONVERSATION WITH NOAM CHOMSKY" A FEATURE BY MICHEL GONDRY
THE TEN SHORTS BEING CONSIDERED FOR THE OSCAR FOR BEST ANIMATED SHORT
THE ACADEMY HAS 19 ANIMATED FEATURES TO CONSIDER FOR THEIR FIVE NOMINATIONS
SEVEN NEW BOOKS OUT ABOUT ANIMATION YOU MIGHT WANT TO CONSIDER BUYING
ONCE AGAIN QUESTIONS ARE BEING RAISED ABOUT OVERLAP IN OSCAR CATEGORIES
DREAMWORKS IS DEVELOPING A FEATURE BASED ON A SERIES OF BANNED BOOKS!
JEFFREY KATZENBERG IS AMONG THE TOP HOLLYWOOD SUPPORTERS OF HILLARY CLINTON FOR PRESIDENT IN 2016
HOW SMART IS IT TO START AN ANIMATION BUSINESS IN A FOREIGN COUNTRY?
ANIMATION'S HOME ON THE RANGE IN SOUTH DAKOTA
MIXING ANIMATION AND LIVE ACTION FILMS MAKES A TASTY FEAST FOR THE EYES. THE FESTIVAL INTERNATIONAL du COURT METRAGE,
"MY MOMMY IS IN AMERICA AND SHE MET BUFFALO BILL" REVIEW
Myths of Mass Deception ~ Thanksgiving ~ Christmas
Click to open Christmas
while wondering where convenient, corporate media, patriotic, "U.S.A." chants are, as holiday bulk profits travel afar?
Paul Krassner ~ The Realist/Writer/Comic/Investigative Satirist
Is There a Doctor in the House?
by Paul Krassner, for AlterNet
Although Coachella Valley in Southern California has become synonymous with music festivals, Goldenvoice, the company that produces those events, also helped sponsor the first massive four-day health clinic this year. Free medical, dental and vision care was provided to nearly 2,500 uninsured patients at the Riverside County Fairgrounds.
According to the California Healthcare Foundation, this state now has the largest number of people without health insurance -- 6.9 million –- more than any state in the country. More than 20% of Californians remain uninsured. Employees in businesses of all sizes are more likely to be uninsured in California than any other state. About 60% of the uninsured population are Latino.
Pamela Congdon, president of the Remote Area Medical’s California affiliate (RAM CA) and Volunteer Coordinator, told me:
“The California Association of Oral and Maxillofacial Surgeons (CALAOMS) helps sponsor RAM CA. They allow us to use their office, use our staff, including myself and our Associate Director, without any charges. I work for CALAOMS, and when I asked if they would help us bring RAM in Northern California, they agreed. Stan Brock asked me to start the affiliate -- RAM CA –- which ran the clinic in Coachella. Please say that the clinic is run by the greatest group of volunteers.”
Indeed, over 1,200 general and healthcare professionals volunteered to provide more than 10,000 individual services with more than $1,000,000 in value. Over those four days, twelve hours a day, an estimated 600 custom pairs of eyeglasses were cut, 750 medical exams administered, and 1,300 dental patients treated.
There were 615 general volunteers, 395 dental professionals, 60 vision professionals, and 190 medical professionals of all kinds. There were 1,766 dental patients, 1,435 medical, and 798 vision. One patient hadn’t seen a doctor for seventeen years. Of the 2,419 patients, 1796 were Latino. Oh, yes, and 234 stuffed animals were handed out to children.
One patient sent this message:
“My name is Jennifer and I wanted to say thank you from the deepest of my heart! I found out about RAM in Indio at 11 p.m. on Thursday. By 2:30 a.m., I had made my way across the valley, and joined in line with the rest of the people you helped. Not a SINGLE person I interacted with was anything but kind, courteous, and understanding. No one judged us for being there, no one thought we were a burden.
“I had all of my wisdom teeth pulled, something I avoided due to an overbearing phobia of dentists in general. Both my dentist and the dental assistant were comforting, and made the procedure almost painless, and fast. I am almost in tears as I write this email, due to the overwhelming gratitude I have for everyone involved in this amazing project that has changed and saved so many lives, including my own.”
***
I’m writing this in the middle of the Open Enrollment time frame, during which my wife Nancy and I finally signed up for a Medicare Advantage plan. Stemming from an old police beating, I use a cane to walk from room to room, and a walker outside the house. The new healthcare plan includes free access to a gym, and I picture myself using my walker on a treadmill. That image reminds me of a New Yorker cartoon depicting a group of people on stationery bicycles in a park.
In the process of enrolling in the Medicare Advantage plan, we were told that we would have to pay a penalty because we hadn't joined a Medicare (or any other “creditable”) prescription drug coverage. We were never informed about that requirement, which began in 2006.
Since we’ve always avoided taking prescription drugs, we never felt the need for it. I called the Health Insurance Counseling Advocacy Program and learned that the penalty would be $32 for each of us. That means $64 every month for the rest of our lives. It seems somewhat absurd and unfair that we could be penalized for not taking any prescription drugs.
Ironically, “This penalty is required by law is designed to encourage people to enroll in a Medicare Drug Plan when they are first eligible,” yet we had no way of knowing there was such an option to consider. Another irony is that Medicare doesn’t cover any dental procedures, even though rotten teeth and gums can cause internal illness that Medicare does cover.
I asked RAM CA volunteer Dr. Peter Scheer, a world-renowned oral surgeon, about that. His response:
“In regard to Medicare and covering dental needs, it has always been an issue. Medicare stands strong in only providing benefits for services that are deemed medically necessary and has always excluded anything related to dentistry, surgical or restorative.
“Yes, there are situations where a patient may have an atrocious dental infection that can become life-threatening if not treated. The times where this situation really hits a grey area is when the patient also has other medical issues that may be affected by the infection or contributing to it. Unfortunately, most instances we come across are a decrease in the quality of life due to a poor oral condition rather than a life-threatening event.”
However, a research team from Columbia University’s School of Public Health has just released the results of a three-year study of 420 men and women, concluding that the improvement of gum health can help slow the development of arteriosclerosis, the build-up of cholesterol-rich plaque along artery walls, which can lead to heart attacks and strokes.
Meanwhile, Goldenvoice has invited RAM CA to return next year. I asked Pamela Congdon, “Will the Affordable Care Act affect that event, or is it too early to tell?” She replied, “The ACA won’t affect the event in terms of people needing service. We are going to have the Borrego Community Health Foundation there to help people sign up for the ACA.” As inspiring as this year’s four-day free clinic has been, in a truly compassionate culture, there would be no need for its existence.
But the insurance industry has a pre-existing condition known in technical terminology as greed. Not to mention the pharmaceutical industry; the annual turnover of revenue for prescription drugs by the top ten companies is estimated to be worth $700-billion dollars. In my new Medicare Advantage Enrollment Kit, there are listed a few thousand prescription drugs, from Abacavir to Zyvox. Okay, now cue that soothing voiceover to recite all their side effects, from anal leakage to zits.
As for me, I owe my longevity to never taking any legal drugs.
Freedom of expression and freedom of speech aren't really important unless they're heard...It's hard for me to stay silent when I keep hearing that peace is only attainable through war. And there's nothing more scary than watching ignorance in action. So I dedicated this Emmy to all the people who feel compelled to speak out and not afraid to speak to power and won't shut up and refuse to be silenced. ~ Tom Smothers
Cree Prophecy
Only after the last tree has been cut down,
Only after the last river has been poisoned,
Only after the last fish has been caught,
Only then will you find money cannot be eaten.
Closing Argument
None of the Above
Should be a choice on Voter Ballots
Oh, I hope that I see you again I never even caught your name As you looked through my window pane ~~ So I'm writing this message today I'm thinking that you'll have a way Of hearing the notes in my tune ~~ Where are you going? Where have you been? I can imagine other worlds you have seen ~~ Beautiful faces and music so serene ~~ So I do hope I see you again My universal citizen You went as quickly as you came ~~ You know the power Your love is right You have good reason To stay out of sight ~~ But break our illusions and help us Be the light ~ Message by Michael Pinder
Without love in the dream, it will never come true. ~ Jerry Garcia/Robert Hunter
The man whispered, "God, speak to me" and a meadowlark sang. But the man did not hear.
So the man yelled "God, speak to me" and the thunder rolled across the sky. But the man did not listen.
The man looked around and said, "God let me see you" and a star shined brightly. But the man did not notice.
And the man shouted, "God show me a miracle" and a life was born. But the man did not know.
So the man cried out in despair, "Touch me God, and let me know you are there"
Whereupon God reached down and touched the man. But the man brushed the butterfly away and walked on.
Don't miss out on a blessing because it isn't packaged the way you expect.
Internet
1991-2013
Destroyed by the: Bush Administration, Obama Administration, and Evil,
Greedy Corporations who had NOTHING to do with Internet Construction
(fwiw)